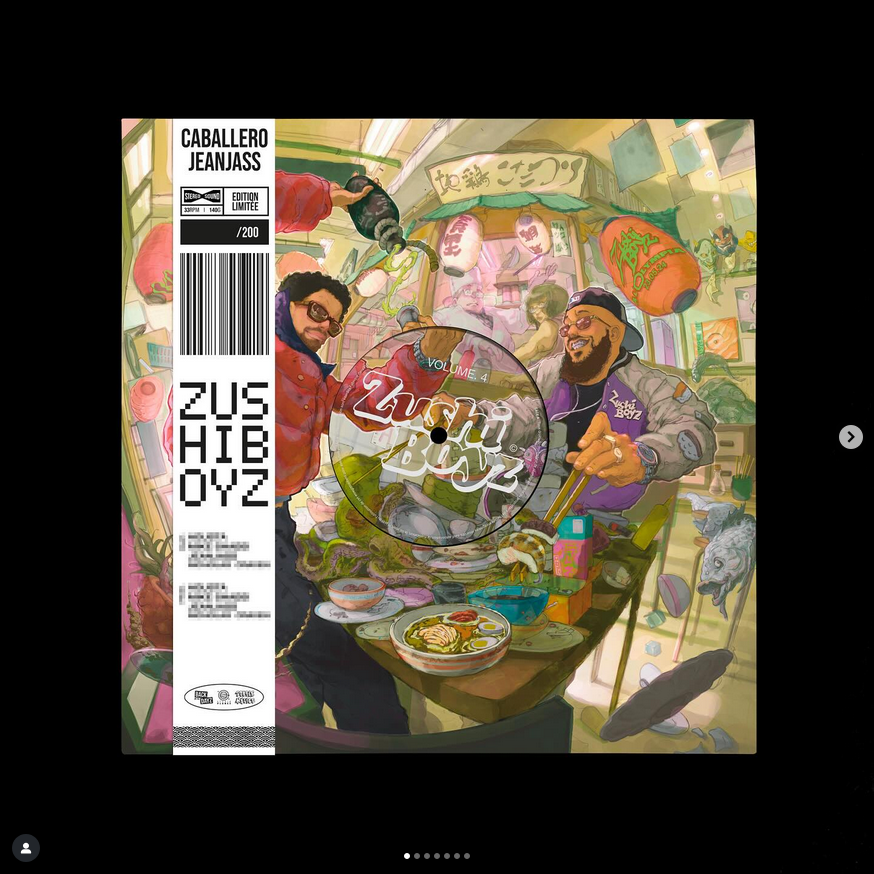
Caballero & Jeanjass - ZushiBoyz vol.4 - Edition exclusive (avec OBI)

Rounhaa - Jaafar

ZushiBoyz vol.3 - Edition exclusive (avec OBI)
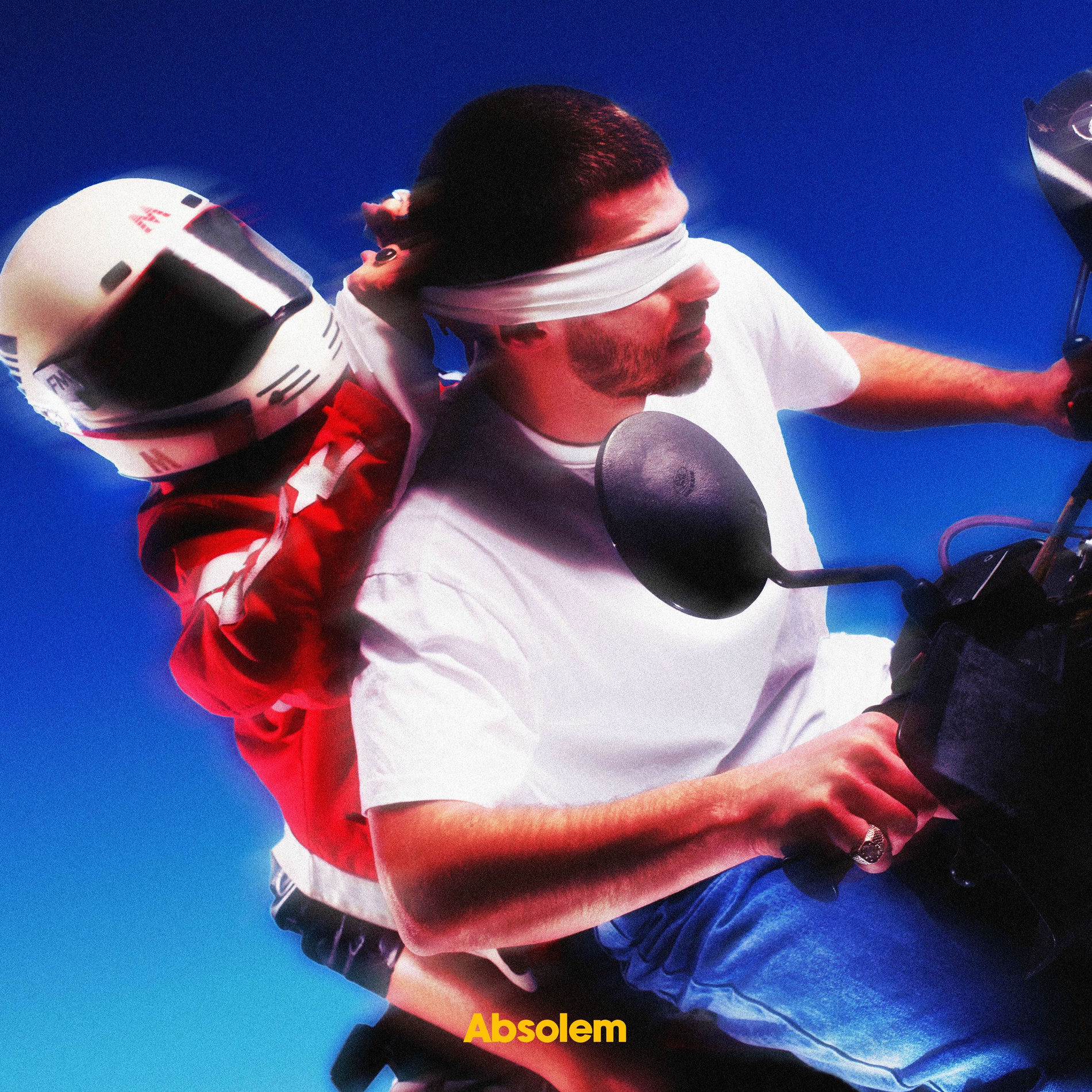
Absolem - Les yeux grands fermés

Al-Walid - Sarman??

Alpha Wann - Don Dada Mixtape
Alpha Wann - UMLA

Beeby - Gaia

Beeby - Morningstar

Beeby - UN GRAND CŒUR DANS UN MONDE DE FILS DE PUTE

Bushi - Bushi Tape 3

Caballero & Jeanjass - DOuble Helice 3

Caballero & Jeanjass - High & Fines Herbes
Caballero & Jeanjass - Zushiboyz Vol .1
Caballero & Jeanjass - Zushiboyz Vol.2

Caballero - Dose Heroique
Chavi & Guydelafonsdal - Chavidelafonsdal
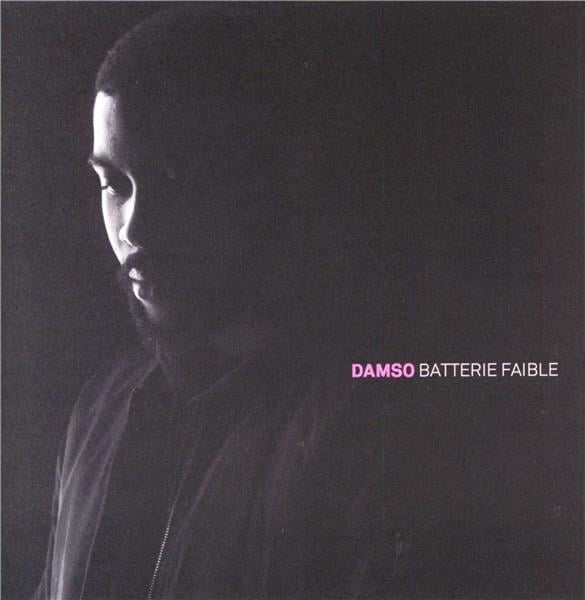
Damso - Batterie Faible
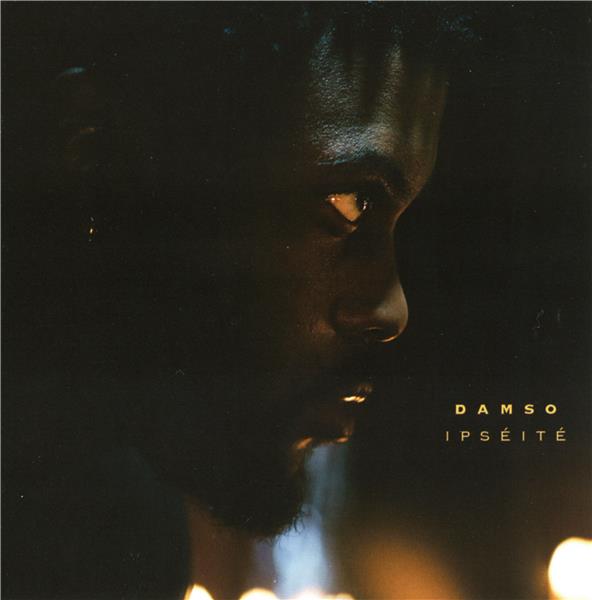
Damso - Ipseite
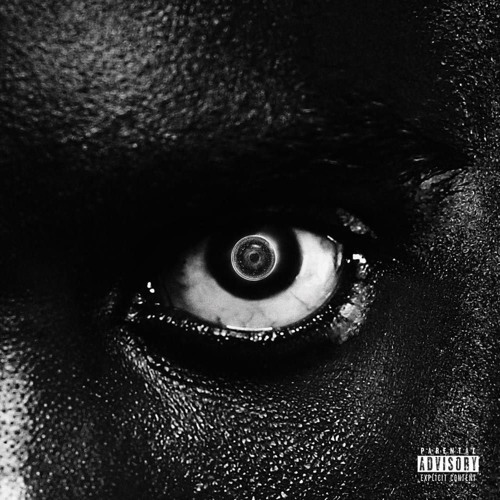
Damso - Lithopedion
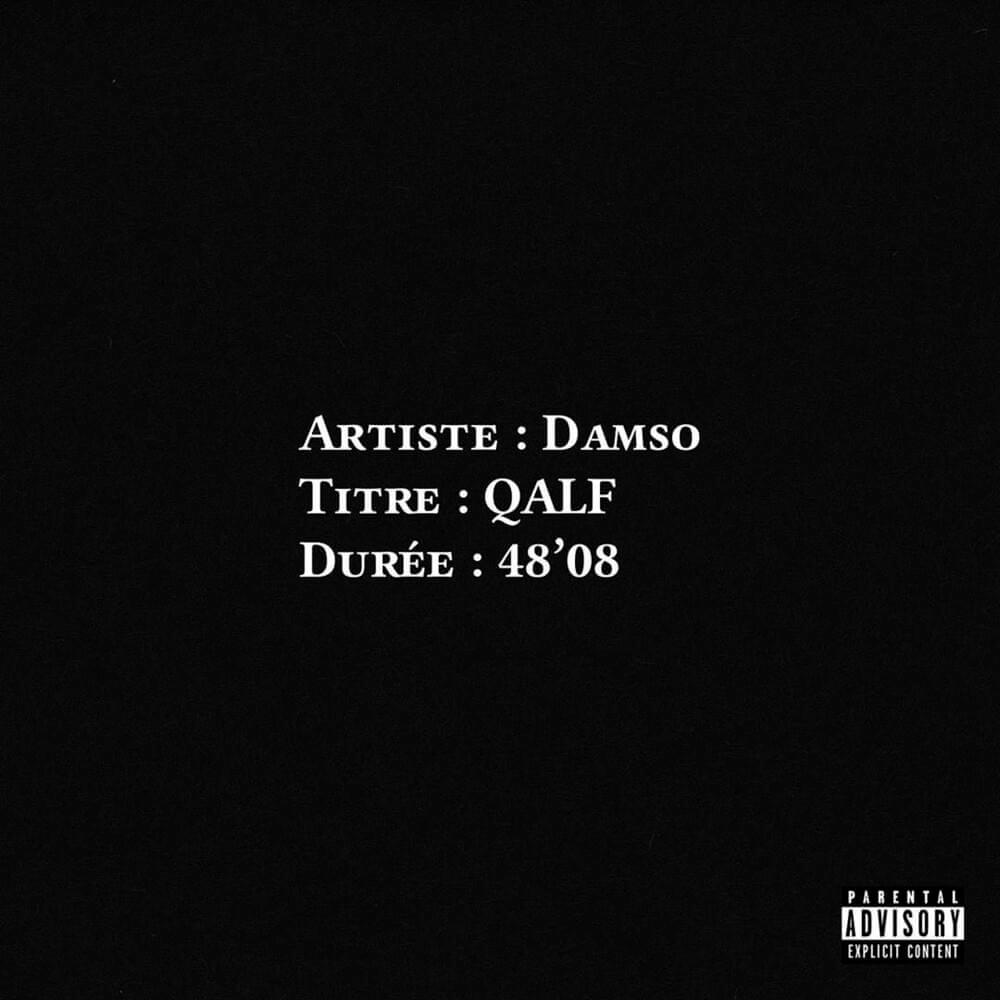
Damso - QALF

Deen Burbigo - Cercle Vertueux

Deen Burbigo - OG SAN 1
Deen Burbigo -OG SAN 2
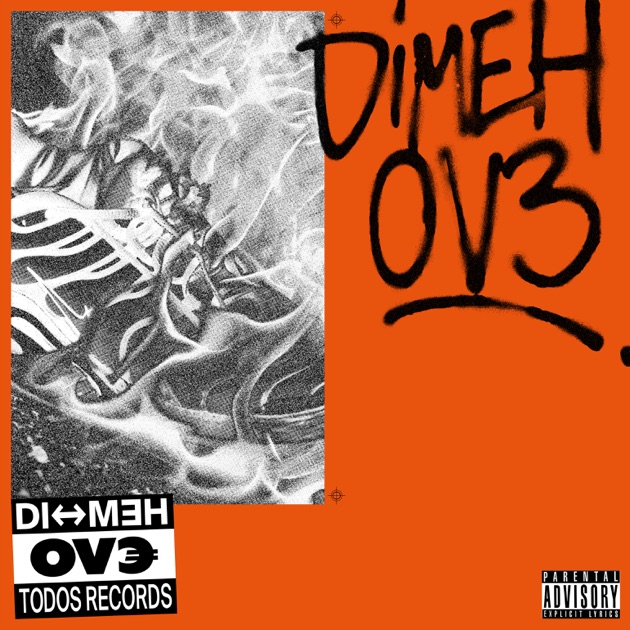
Dimeh - OV3

GAL - Du Caviar Pour Mon Chien

GAL - JeuneBeurdelafontaine vol2
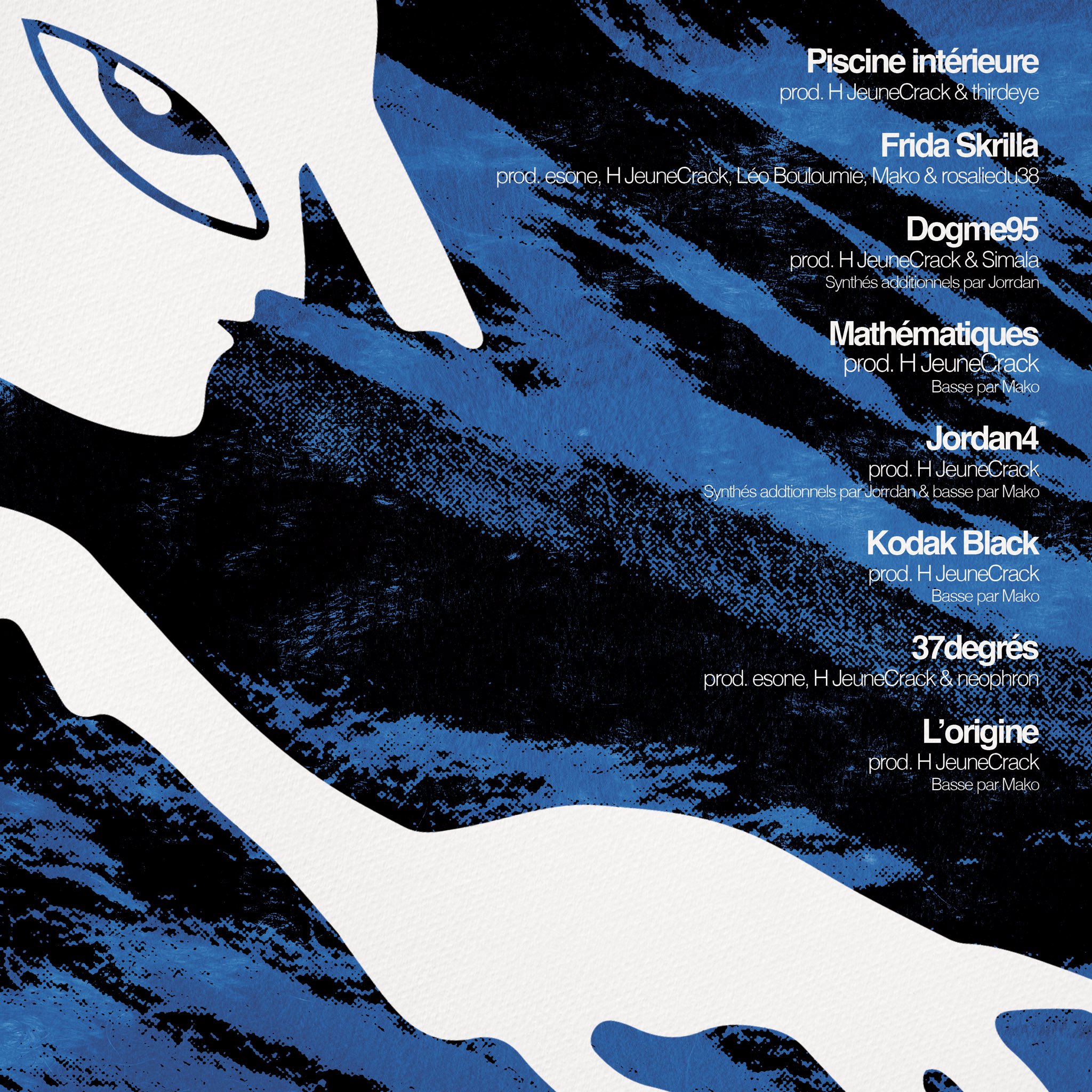
HJeuneCrack - 2eme Mouvement

HJeuneCrack - La Pieuvre

HJeuneCrack - Matiere Premiere

HJeunecrack - 1er Mouvement

HJeunecrack - 3eme Cycle

Hamza -1994

Hamza -Paradise
Huntrill - LE BRUIT DE LA MACHINE A BILLETS
Huntrill - Replica 2
Infinit - 888

Infinit - Ma vie est un film 2

Infinit - Mr Le Faire
Isha & Limsa D'Aulnay - Bitume caviar

JUngle Jack - Jungle des illusions Vol 2
JeanJass - Goldman
Jeanjass - Doudoune en été
Jeanjass - Tous ces ongles rongés
Jok'AIr - Jok'Rambo

Jok'Air - Jok'Chirac

Jok'Air - Jok'Travolta

Jok'Air - New Jok City
Josman - J.000.$

Josman - J.O.$

Josman - M.A.N (Black Roses & Lost Feelings)

Josman - MYSTR J.O.$
Josman - SPLIT
Jungle Jack - Cognacs et Cigarette
Jungle Jack - Creamland

Jungle Jack - Jungle des illusions

Juwel Usain - Ou les garcons grandissent
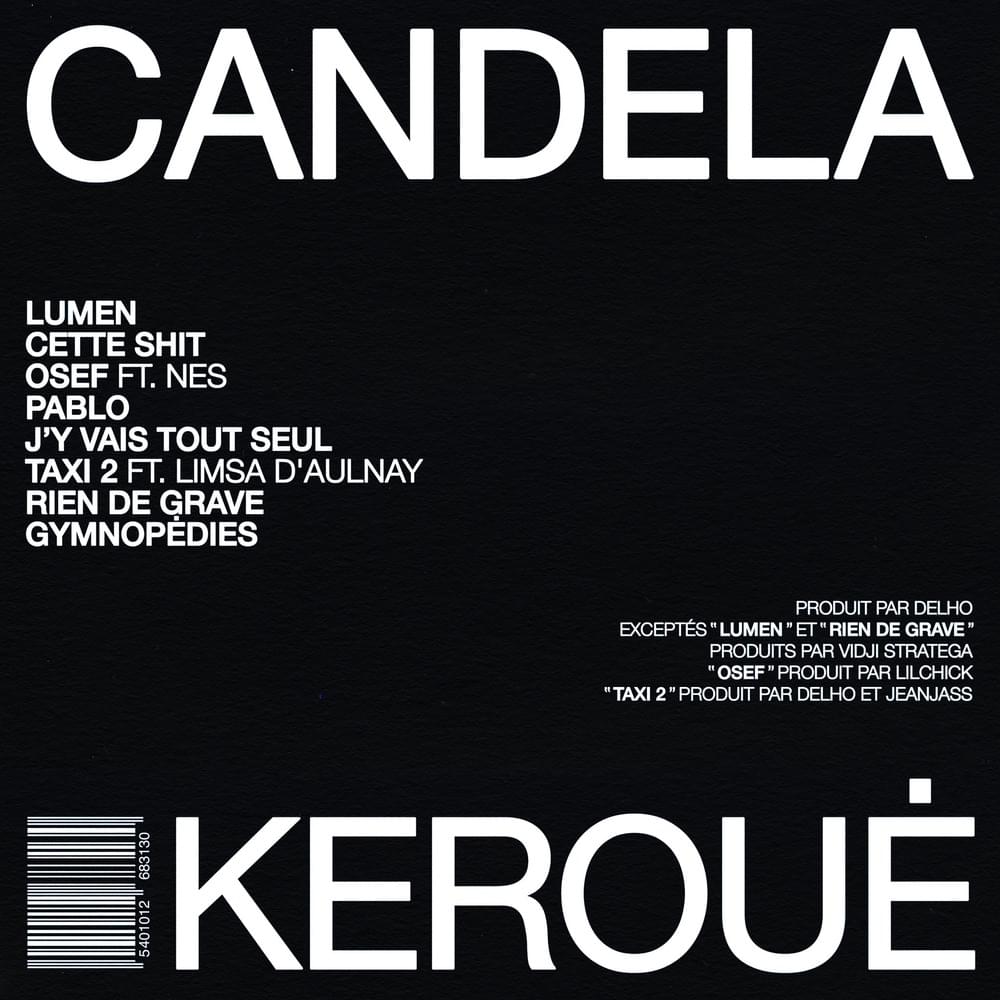
Keroue - Candella
Keroue - Record

Keroue - Scope

LaFeve - 24

LaFeve - ERRR
Le Monde Daho - Le Monde 00
Ledouble & Guydelafonsdal - LeDoubledelafonsdal
Lefa - Fame

Lefa -3 du mat

Lefa-DMNR

Luidji - Boscolo Exedra
Luidji - Saison 00

Luidji - Tristesse Business

Luther - EXIT

Luther - Garçon

Mairo - Omar Chappier

Mairo - Dejeuner en paix

Mairo, H JeuneCrack - La solution
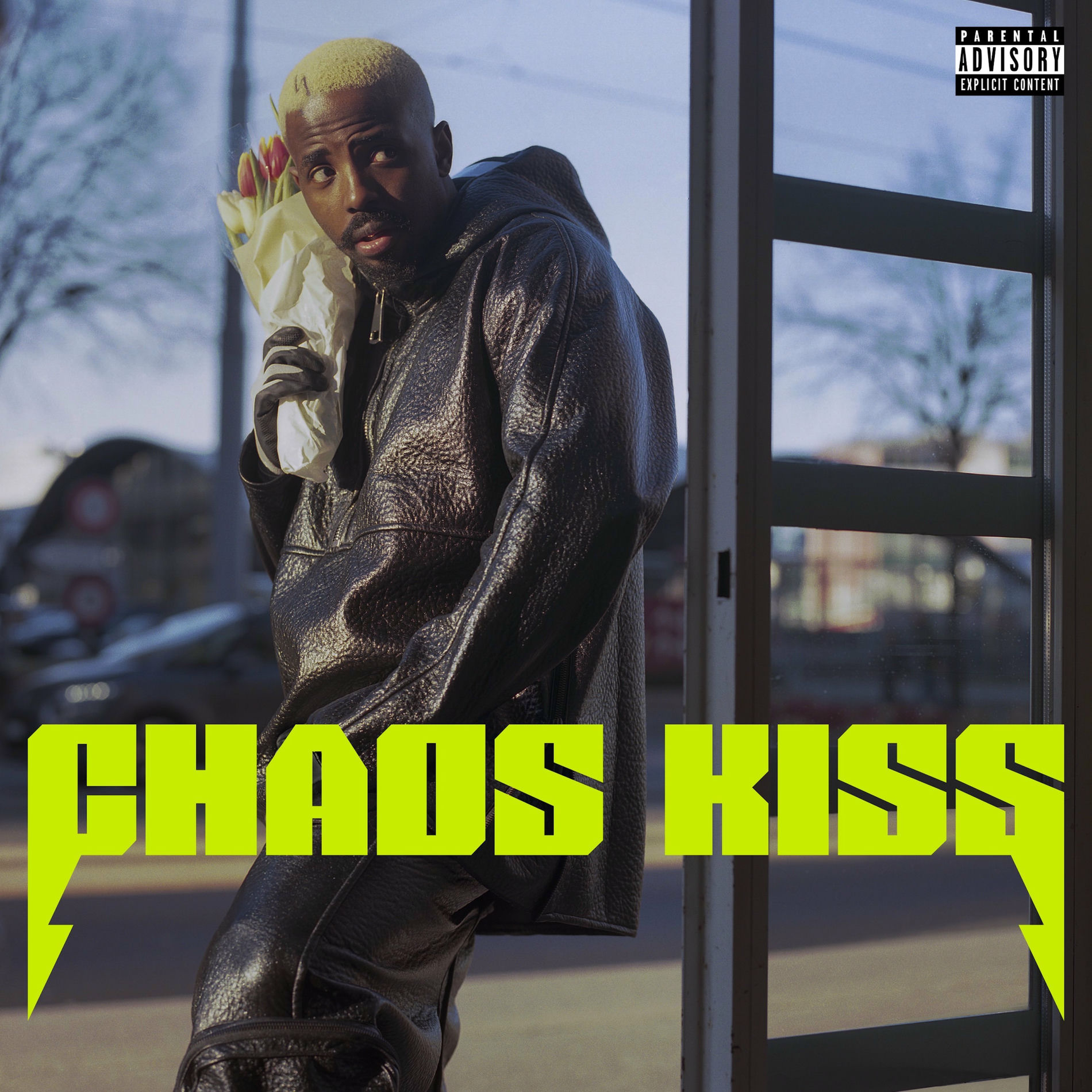
Makala - Chaos Kiss
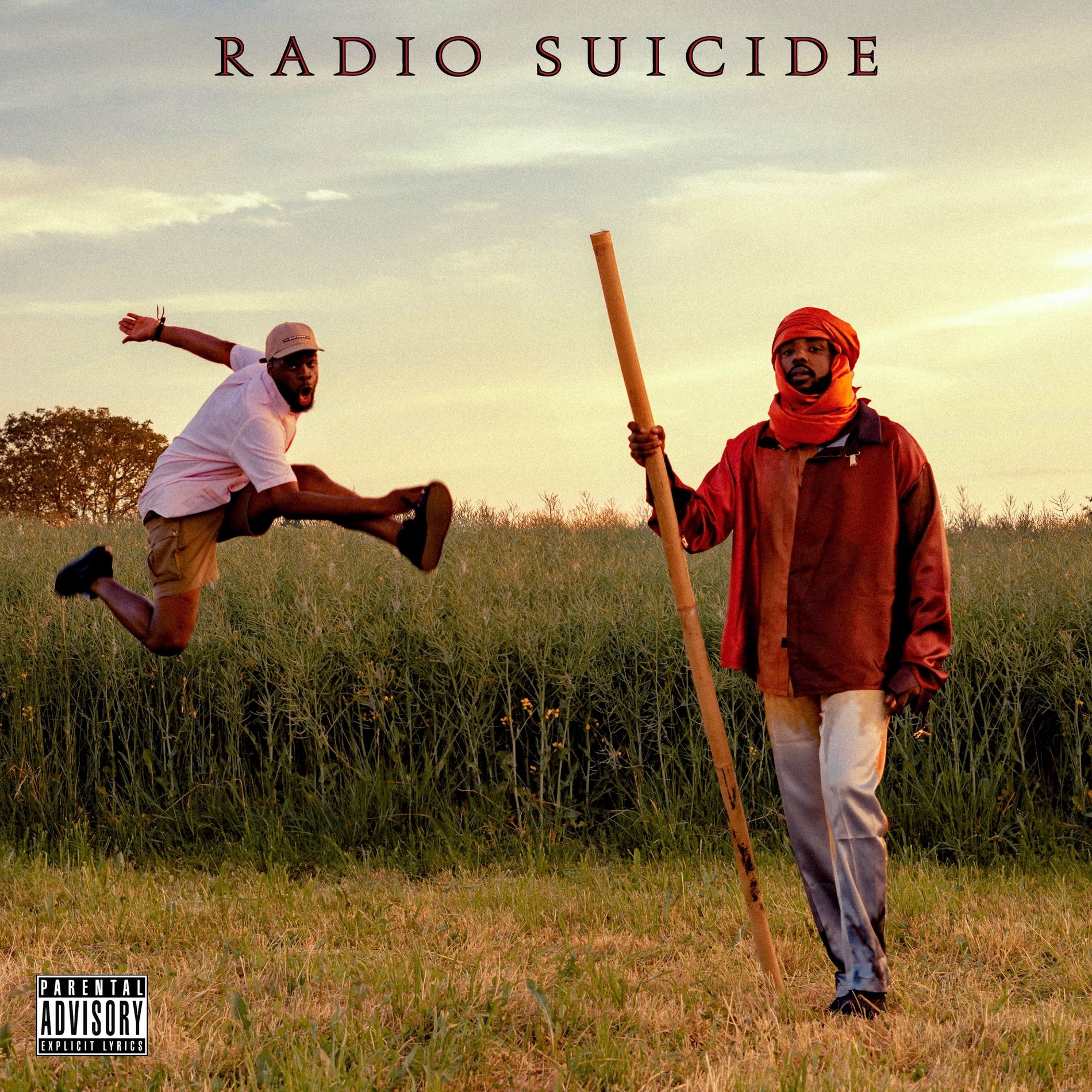
Makala - Radio Suicide

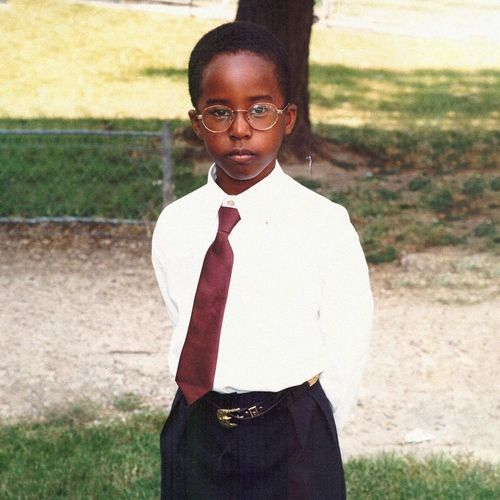
Makala - Yamoto
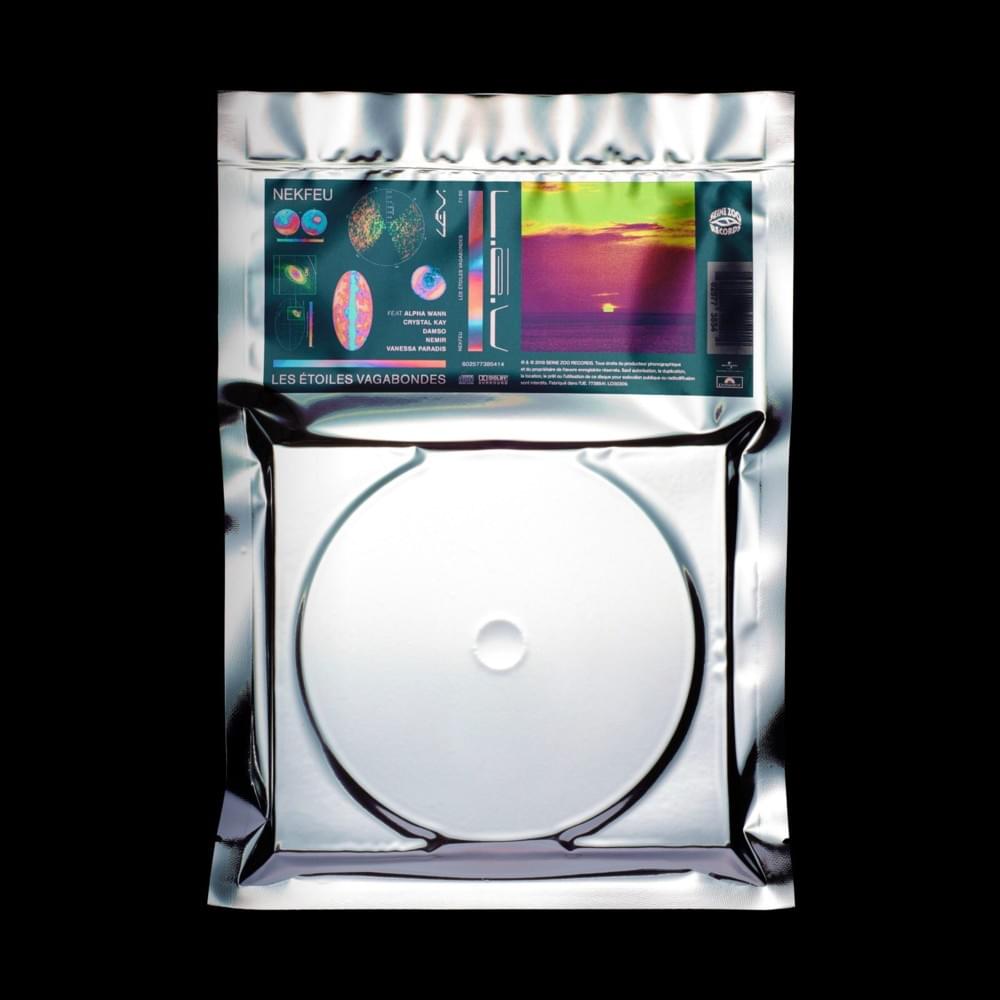
Nekfeu - LEV
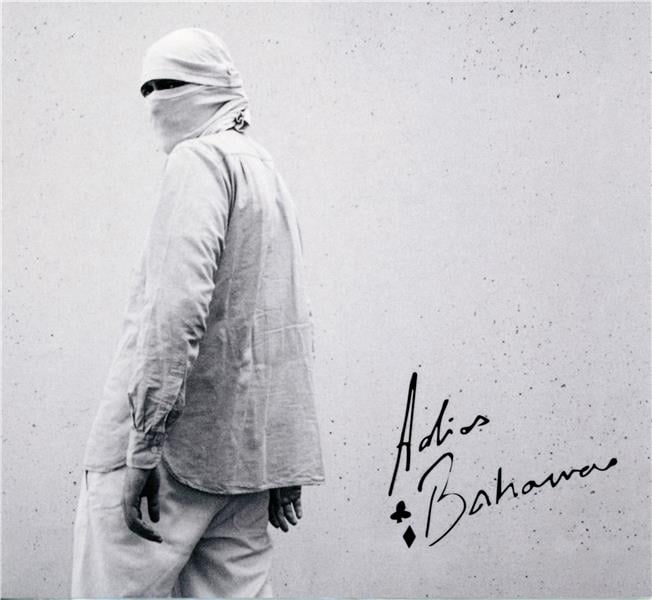
Nepal - Adios Bahamas
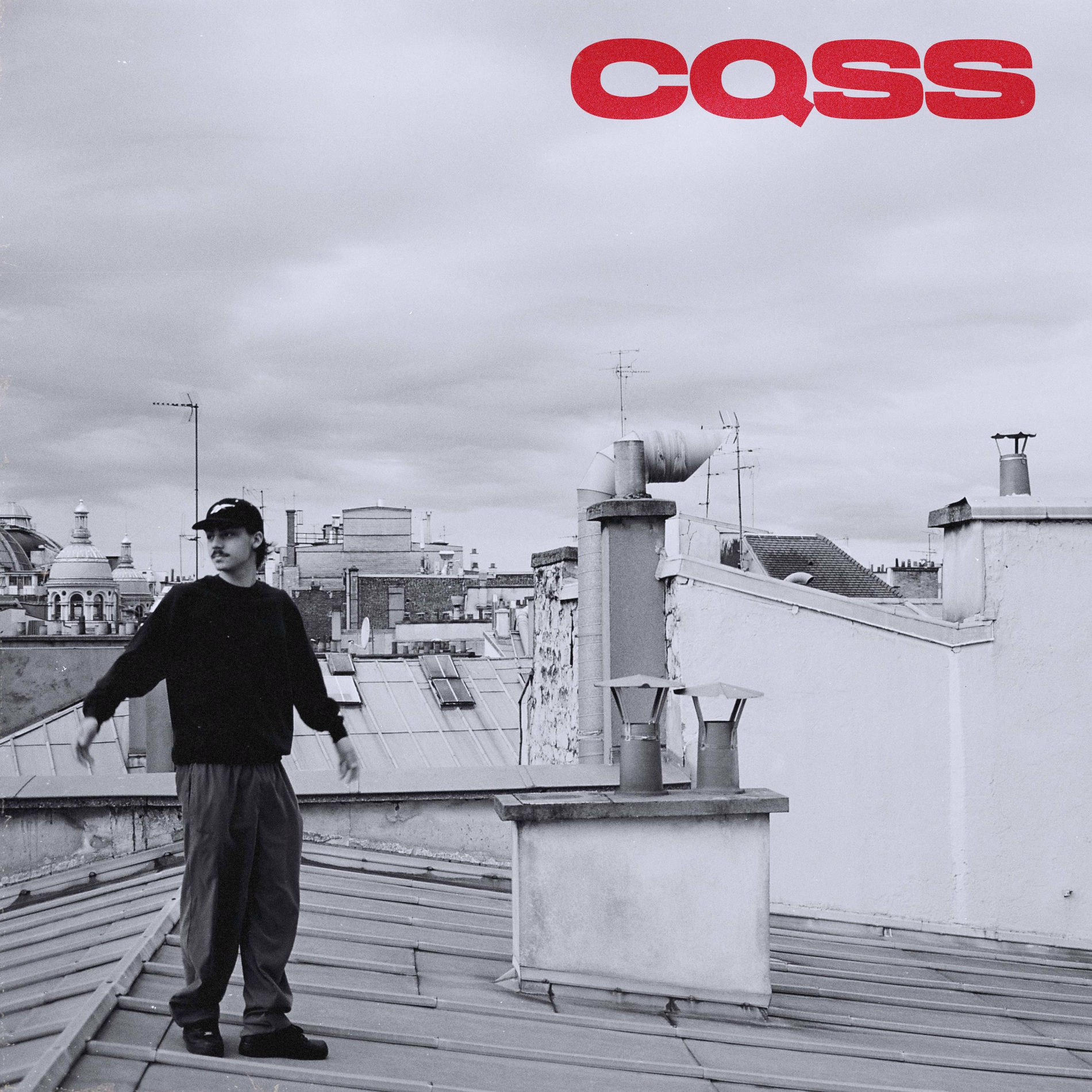
Nes - CQSS
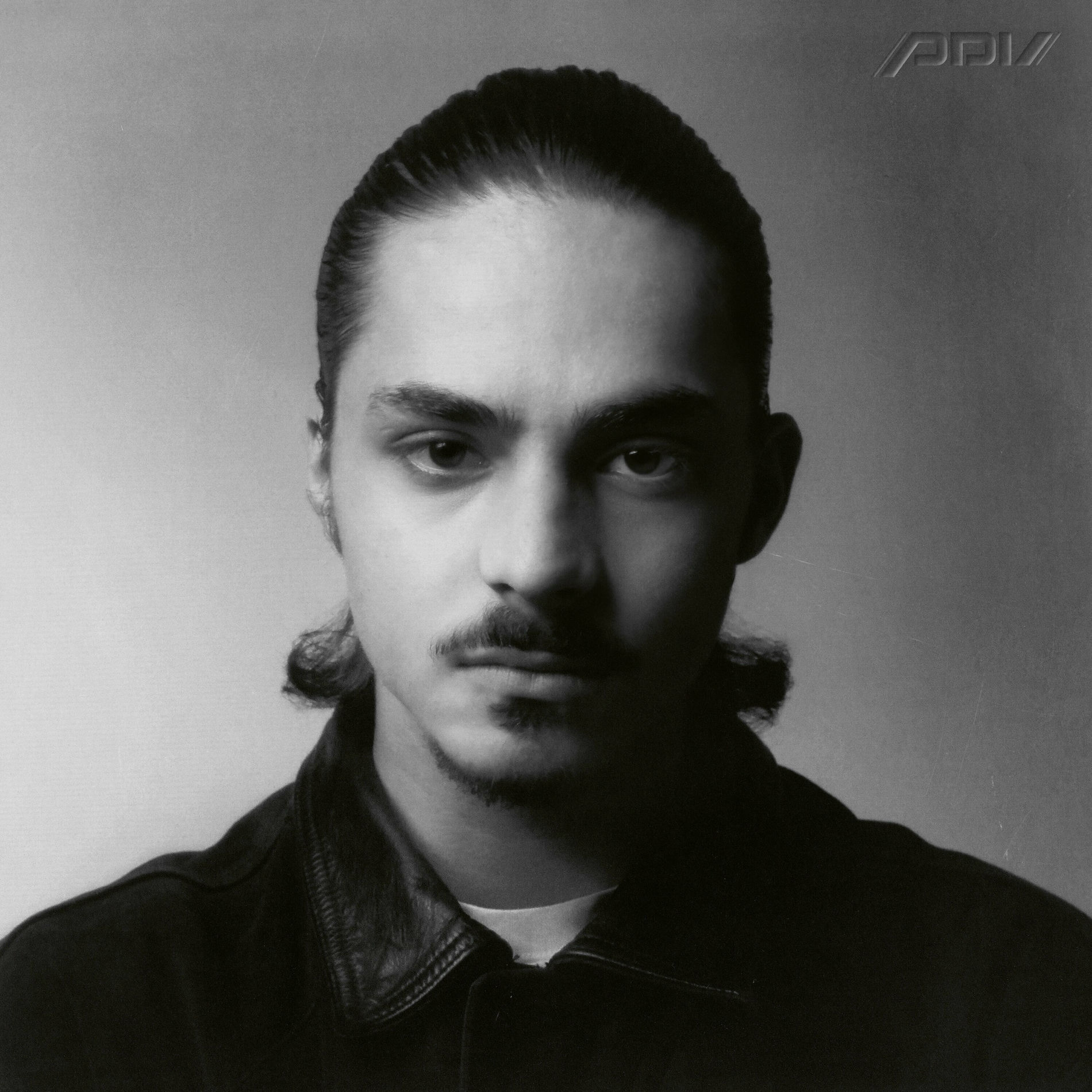
Nes - LA COURSE
Nes - Pour 2 VRAI

Nes - ÇA VA ALLER

Nujabes - MetaphoricalMusic
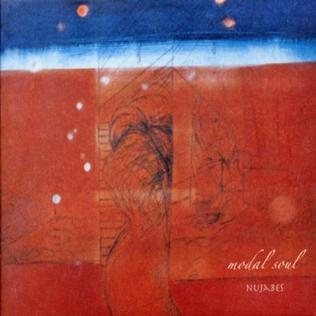
Nujabes - Modal Music

Nujabes - departure

OgLounis & Guydelafonsdal - OgLounisdelafonsdal
Oglounis - HARD LAIDBACKING BEFORE

Prince Wally - Moussa

Romeo Elvis - Chocolat

Romeo Elvis - Tout Peut Arriver
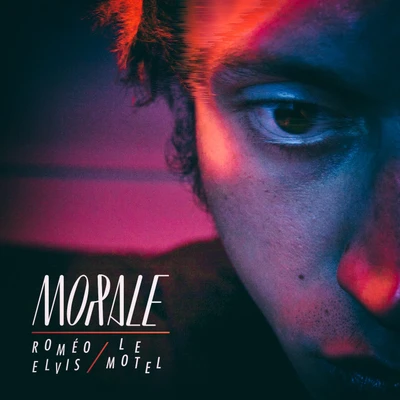
Romeo Elvis Morale

Selug & Kyo Itachi - TATAKAE

Slimka - Le Grand Mystico

Tisma & Guydelafonsdal - Tismadelafonsdal

Toothpick & Guydelafonsdal - Toothpickdelafonsdal
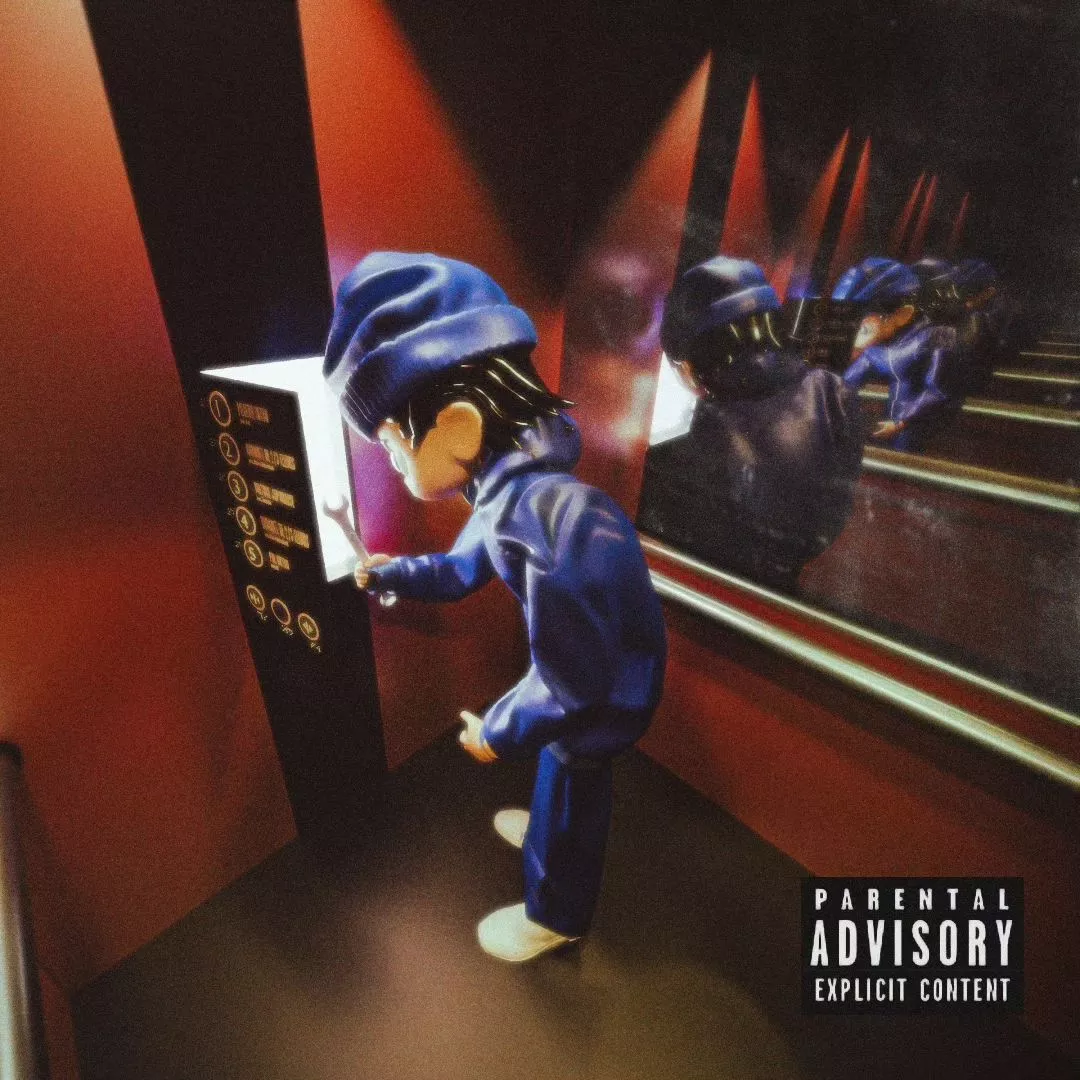
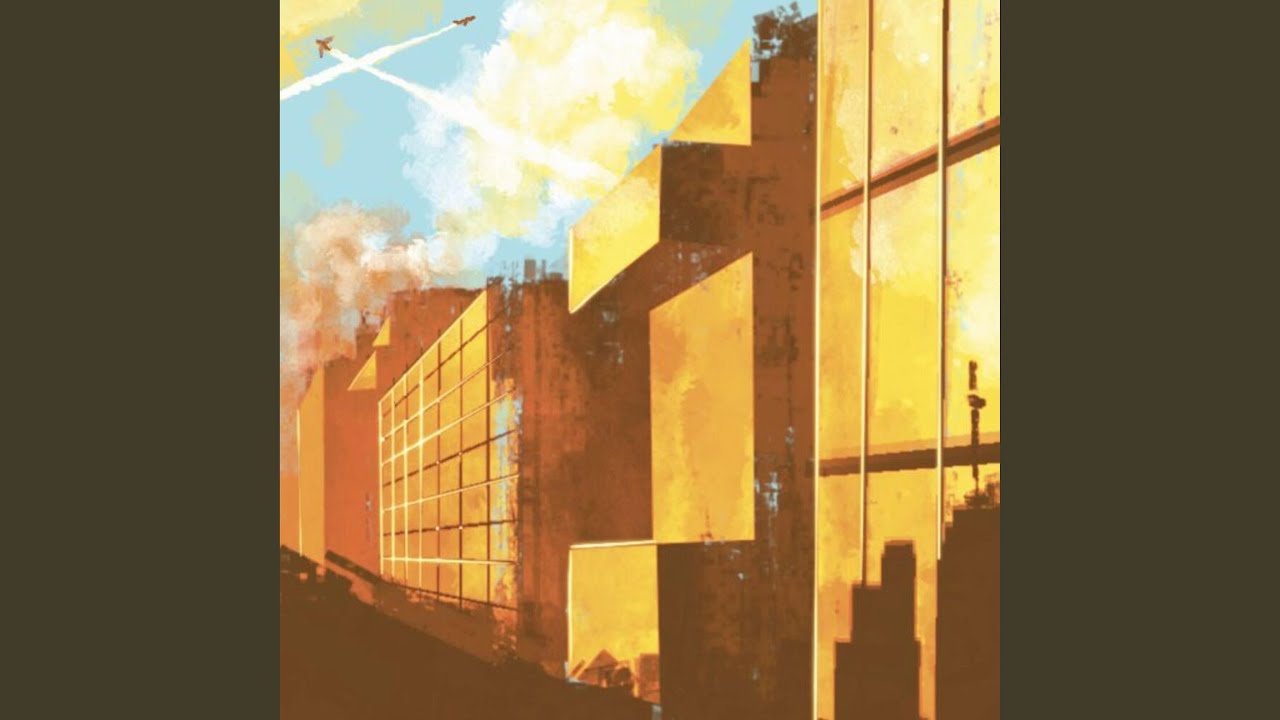
Toothpick - JEUNE LIFTIER

Toothpick x 3.14 - No Casquette Vol.1
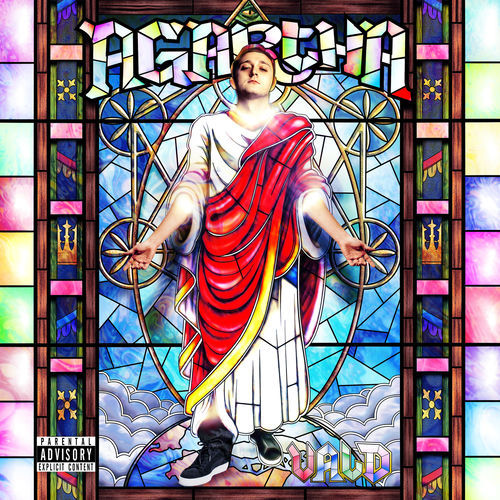
Vald - Agartha

Vald - Ce Monde Est Cruel

Vald - V
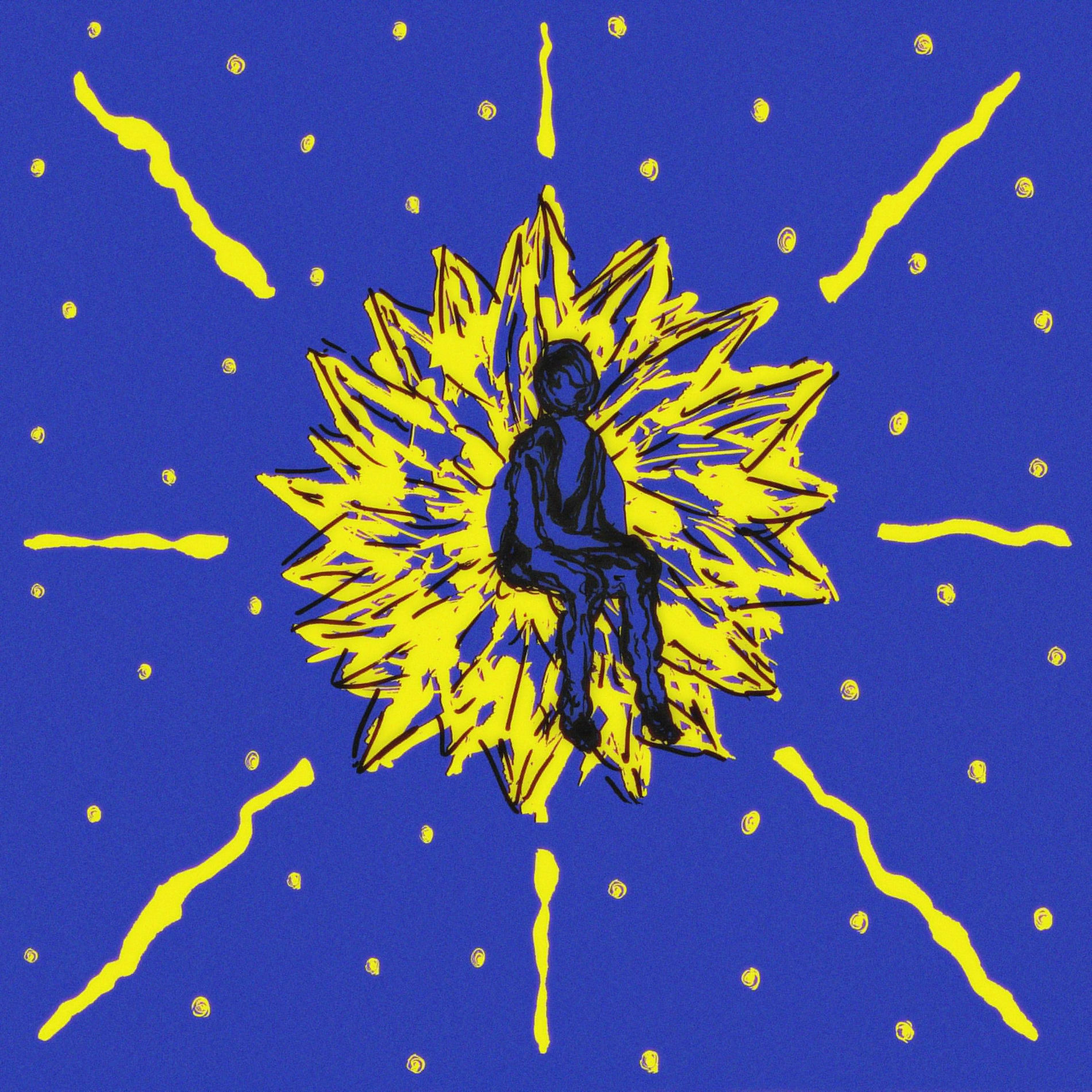
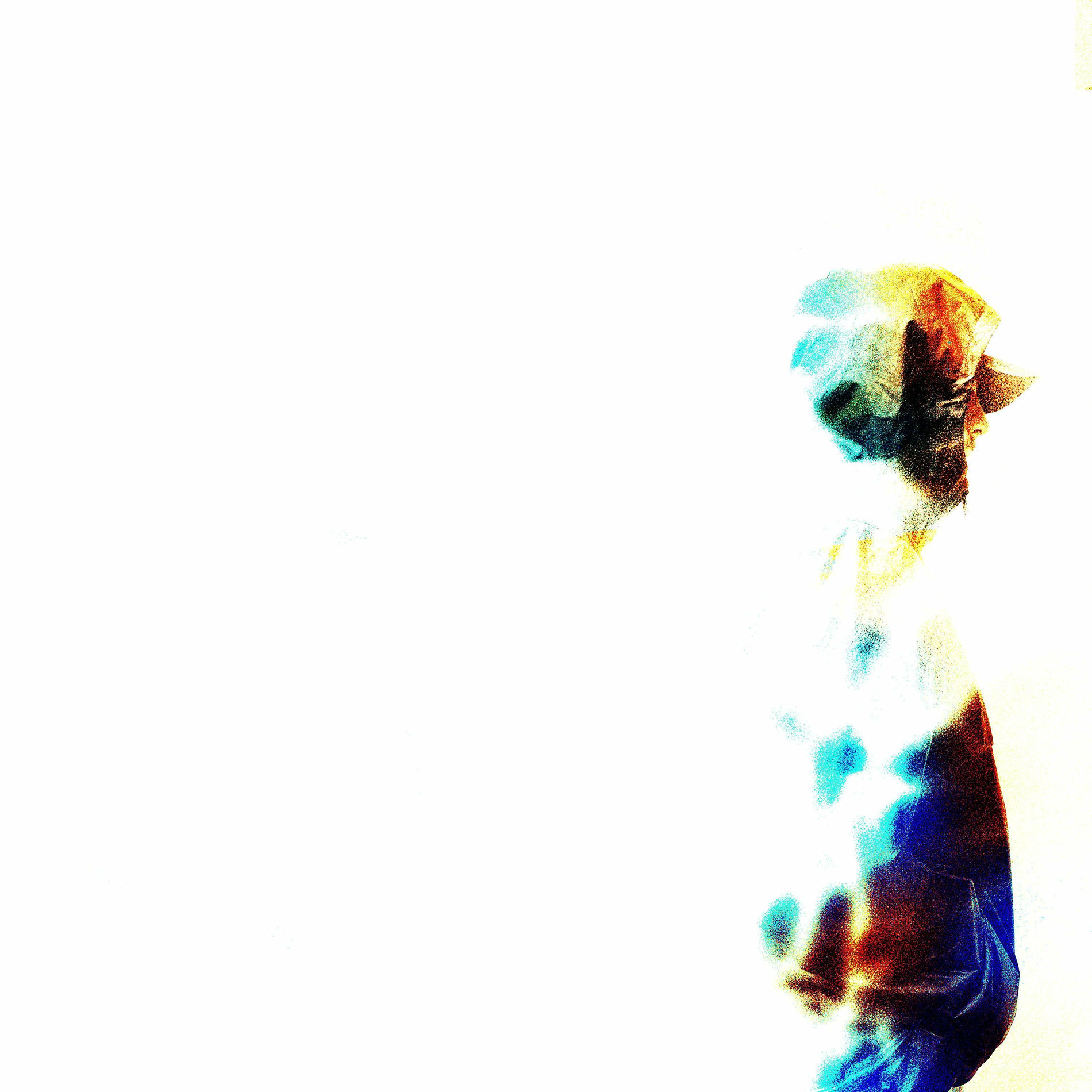
Yvnnis - NOVAE

Zushiboyz (Info)

a5el - Mercenaire

okis & Mani Deïz - Rêve d'un rouilleur